Apparent cyber attack sheds light on village security
Unusual FOIL request traced to Russian server
The Village of Rockville Centre appears to have been the victim of a broadly targeted cyber attack last month originating from a server in Russia, though cybersecurity experts said the attempt was most likely unsuccessful.
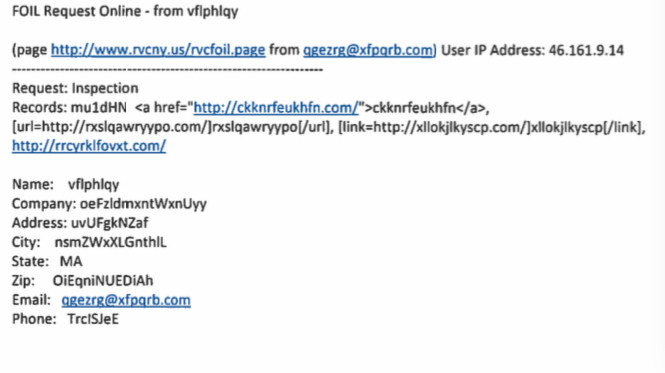
The attack was made using a form on the village’s website — www.rvcny.us — where public records can be requested under the state’s Freedom of Information Law. A document obtained by the Herald under that law showed the details of a July 9 FOIL request, which contained a number of unusual elements.
The user filled out the form with the name “vflphlqy,” and the zip code was “OiEqniNUEDiAh.” In the box where users write in their requests, the user attempted to insert code that would produce links to web addresses with more random strings of letters. The links are now defunct.
The request came from a server in Russia, according to the IP, or Internet Protocol, address listed in the document. This server has made more than 22,000 attacks since last October, peaking at 615 attacks in a single day in March, according to StopForumSpam.com, one of many websites that track “toxic” IP addresses.
Using what’s called a “WHOIS Lookup,” a method of tracing domain names and IP addresses through the Internet Corporation for Assigned Names and Numbers, it appears that the server is owned by a company under the name Bashilov Jurij Alekseevich. The company owns 57 servers, according to IP database MyIP.ms, most of which are associated with several cases of reported abuse.
Xiang Fu, a computer science professor and cybersecurity specialist at Hofstra, said that it appeared the server was “penetration testing,” an industry term meaning that it was searching for vulnerabilities. “If a system behaves OK, they’ll leave it alone,” Fu said. “If the system crashes or behaves differently, they’ll continue and exploit that vulnerability and turn it into something more useful for them.”
There is no way to know exactly what kind of attack this was, according to Fu. “My sense is that the attacker is not close to success yet,” he said.
Rockville Centre native Michael Salsone, a computer security engineer, agreed with Fu’s assessment, adding that input like this typically comes from automated web robots, or bots, “that go around submitting every form they can find, and putting malicious links into them.”
Just because the request originated from a server in Russia, Salsone said, does not necessarily mean that Russians are behind the attack. “WHOIS information is OK,” he said. “But typically it’s either shielded or unreliable.”
The village is no stranger to cybersecurity. “We are consistently evolving and adapting to changing cyber threats,” said spokeswoman Julie Scully. “We continue to be proactive and adopt strategic strategies that swiftly identify and respond to digital security risks.”
The July 9 FOIL request is the only documented case since January of a malicious use of the village’s online form. The Herald requested older records that might contain similarly suspicious entries, but the village is not bound by law to retain FOIL requests older than six months.
The village’s security systems have blocked almost 2 million emails to date, Scully said, including some that turned out not to be malicious. Sometimes, she said, a legitimate email gets caught up in the filters, and information technology professionals must manually allow the message to pass through. Additionally, Scully added, filters on the village website have blocked nearly 14 million requests, including spyware and viruses.
Even when malicious material passes through the filters, as the suspicious FOIL request did, there is usually a human barrier that Scully called “the last line of defense.” She said that village employees are trained in basic cybersecurity, adding that they are instructed not to open email attachments unless they are expecting an email from a specific sender.
According to Salsone, there is an easy way to prevent bots like this one from ever making it past the submit button. “Captchas are typically very good at stopping bots,” he said, referring to simple tests that many online forms use to ensure that their users are human. He added, “I think they’d be worth using for this case.”
Scully said that the village uses captchas on some of the website’s forms, like the “Contact Us” page, for example, and that it plans to soon implement them on all of its website forms.
The village’s cybersecurity philosophy is simple, Scully said: “An ounce of prevention is worth a pound of cure.”